There’s a new crypto locker virus called Osiris that is easily slipping past the current generation of malware prevention software. Osiris is typically infecting computers as an attachment to emails. Fortunately, there are multiple things users can do to protect themselves and recover from these types of viruses.
What is Osiris Cryptolocker Virus / Ransomware?
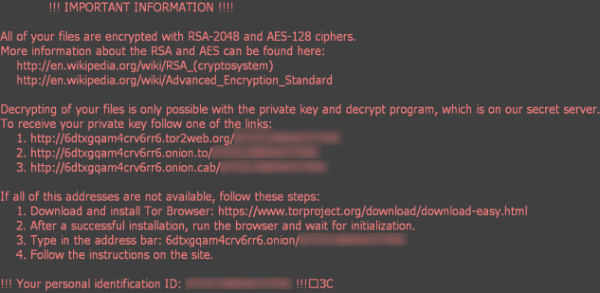
Osiris is known as a cryptolocker virus. It’s a form of ransomware that demands payment after locking up a user’s files. A cryptolocker uses impenetrable cryptographic code to encrypt files on a person’s computer. The hackers behind these viruses demand a ransom to unlock the infected computer’s files. But paying the ransom (usually through the cryptocurrency Bitcoin) is not a guarantee that your files will be unlocked. There have been many reports that people have not received the decryption key even after paying the ransom. Osiris Ransomware is the advanced version of previous Odin Ransomware and Zepto Ransomware which were based on the Locky Ransomware. It can infect Windows, Mac and Android OS.
How does the Osiris Ransomware infect computers?
Osiris targets individual email accounts, either through web browsers or offline mail clients. It’s uncommon to get personally addressed email from someone you don’t know. It’s equally uncommon to have someone you don’t know forward you an attachment file. Osiris will appear as an innocuous attachment to an email that looks like it’s been sent through a reputable company. A favorite ploy is to say that a UPS or USPS delivery has been diverted and needs further action on your part. The only safe course of action in these situations is to not click on email attachments. The virus creators want to entice you to click on the attachment (usually camouflaged to look like a Word document / Excel Sheet or some other trusted file format).
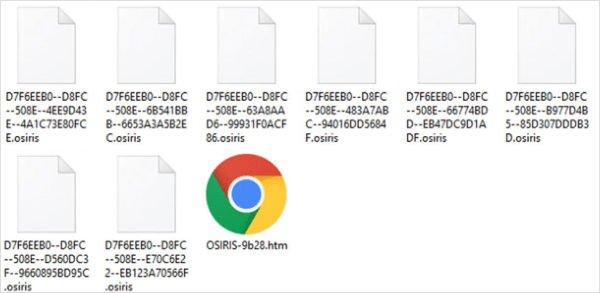
The trouble happens when you click on the attachment. The actual virus payload is always delivered the same way. The attachment is actually a Microsoft Word file that runs a macro when opened. This macro is what ultimately downloads the malware. Once the Word file downloads and runs the Osiris malware, all your files on your hard drive get encrypted. Every file on your hard drive is going to have the Osiris extension at the end of it. When you start seeing that “.osiris” file extension everywhere on your hard drive, that means it’s pretty much game over. Osiris will post a ransomware message on your screen as it’s finishing its job of encrypting your hard drive. If a cryptolocker virus like Osiris infects your computer, your only options are to recover from a backup or pay the ransom. And as already mentioned, paying the ransom is no guarantee that you’ll even get your files back.
Will antivirus and antimalware catch these cryptolockers?
You don’t want to feel that you’re fully protected just by having antimalware or antivirus on your computer. It’s getting to the point where hackers are finding ways to get around the malware prevention software that’s currently out there. It’s true that antivirus and antimalware programs send updates to patch vulnerabilities, there’s still some lag time between patches where you might be susceptible to new viruses.
How to Remove Osiris Ransomware
Before starting process of how to remove Osiris from computer, read the below instructions carefully.
If you have planned NOT to Pay ransom and want to give it a try to restore your files. But before starting removal process you have to keep in mind that in this removal process you can loose your data / files completely forever.
Please dare to start removal process at your own risk as you can loose your data or any of your important document permanently. After this you can even loose your chance to pay ransom.
Steps to remove Osiris Ransomware and try to recover files
Steps to remove Orisis cryptolocker Virus from computer.
- Download and scan your computer with Hitman Pro and Malwarebytes anti malware software to clean up any trojan, malware from your computer to stop downloading Osiris related malware again on your computer.
- Scan with a Good Antivirus software or with any second opinion scanner.
- By doing these above steps chances are that Osiris infection has get removed, but you can not decrypt the encrypted files. In further steps we will try to recover the files.
- Download ShadowExplorer. Install it and try to restore files with this software.
- If you are unable to recover with the step 4 try to recover files with the System Restore.
- If you are still unable to recover, then the last method you can try is using File Recovery Software like Recuva. You can also use other useful Data Recovery Software.
How to Decrypt / Recover Osiris infected Data
At this moment there is no any decryption tool to recover the osiris infected files. But you can only try to recover your data or try System Restore method.
Protecting from the Osiris virus
To prevent this from happening in the future, make sure your Windows OS is fully up to date. Also, make sure that your operating system is setup to display hidden file extensions to be able to see the true nature of the file. Osiris uses random extensions for its attachment (users have reported .542, .343, .552, .xls, .tdb and .zk). Sometimes the virus has been packaged in a .zip file as it can help avoid detection.
Here are some further tips to help guard against cryptolockers like Osiris.
- Make sure your email provider has good spam and malware filtering. Gmail (and Google Apps for Business) offers some of the strongest filters available.
- You can host your files in the cloud with a provider like Dropbox. Dropbox allows you to recover the most recent versions of your files. That means you’ll be able to access a version before they were encrypted.
- Hopefully, you are also maintaining backups of your data. If you have a recent backup of your data on an external drive, then you can wipe your operating system and start over. You’ll have a fresh computer, but it will take some work setting up all your programs and settings to get back to normal again. Check out Best Free Backup Software
- If you don’t already have a backup plan, you can try an online provider. The backup capabilities provided by Windows 10 will be adequate for most users, but make sure it’s not backing up files too frequently. If the interval between backups is less than an hour, you could be overwriting your good files with the encrypted files.
- Malware prevention programs are still useful defenses against cryptolockers. Even though they aren’t an iron-clad defense, it’s still advisable to install an antimalware program as part of your defense against crypto lockers. MalwareBytes 3.0 now includes anti-malware and anti-ransomware in the same product. Spybot Search and Destroy and HitmanPro.Alert are two other alternatives.
- Although Mac users suffer less from virus intrusions, the Osiris virus can just as easily encrypt Mac computers as well. The program Ransomwhere (available from objective-see.com) is a free program that monitors your hard drive for viral encryptions. The program aims to stop the process before it gets too far into your files.
The best defense against crypto locker viruses like Osiris is common sense. Don’t open emails from people you don’t know. And definitely don’t download anything that isn’t from a trusted source.
Welcome to No Ransom, the place to find the latest decryptors, ransomware removal tools, and information on ransomware protection.